SMEs and the Rising Tide of Ransomware and Targeted Cyber Attacks
In Australia, small and medium-sized businesses (SMBs) are increasingly finding themselves in the crosshairs of cybercriminals. These threats arising are not random but calculated and specific. Cybercriminals are honing their tactics to exploit vulnerabilities within businesses that often lack the cyber resilience of more giant corporations.
The OpenText Cybersecurity Global Ransom Survey revealed that nearly half (46%) of enterprises and SMBs admitted to having suffered a ransomware attack. That’s not a tiny number – your business could be the next victim.
So, in this article, let’s understand:
- The Nature of Cyber Attacks
- Impacts and Consequences
- Emerging Threats in the Cyber World
Ransomware and Targeted Cyber Attacks - What Are They?
Ransomware is a cybersecurity threat involving attackers encrypting information on a system and demanding a ransom for a decryption key. Attackers have developed this attack method further to involve double extortion, where they not only steal data and move it to a different location but also threaten to release it if the company doesn’t pay the ransom.
With the rise of Ransomware as a Service (RaaS), it has become much easier for attackers to launch and maintain ransomware campaigns without developing their code. This allows almost everyone to become an attacker, meaning anyone holding malicious intentions can potentially harm your business.
These attacks are called targeted cyber attacks and have become increasingly sophisticated, often exploiting known vulnerabilities in unpatched systems or using phishing emails as a primary means of entry.
The impact of such attacks is profound; for instance, supply chain attacks extend the damage beyond a single victim, affecting a broader network of businesses and customers, as seen in the 2021 Kaseya attack.
Types of Targeted Cyber Attacks
Every seven minutes, Australian authorities report a new cybercrime. Of the almost 700,000 businesses that experienced cybercrime, 60% of the targeted attacks were against small and medium-sized enterprises.
The prevalence of these crimes has risen, with a 13% increase in cybercrime reports over the previous financial year. Ransomware tops these charts, hailing the most destructive cybercrime threat title due to significant direct and indirect costs to victim organisations and the broader public impact.
Phishing Attacks
These involve sending fraudulent emails that resemble those from reputable sources to trick individuals into revealing sensitive information like passwords and credit card numbers.
Spear Phishing
A more targeted form of phishing is where attackers customise their approach to target specific individuals or organisations, often using personal information to increase their chances of success.
Whaling Attacks
These spear-phishing types are targeted at high-profile individuals like CEOs, often involving extensive research and preparation to seem convincing.
Supply Chain Attacks
Attackers target less secure elements in a supply chain to compromise larger organisations or systems. The Kaseya attack of 2021 notably employed this method.
Man-in-the-Middle (MitM) Attacks
SQL Injection:
Here, attackers exploit vulnerabilities in data-driven applications to insert malicious SQL code into a database, allowing them access to sensitive information.
Denial-of-Service (DoS) and Distributed Denial-of-Service (DDoS) Attacks
These involve overwhelming a system’s resources to make it unavailable to users, often flooding it with excessive requests.
Ransomware Attacks
Involving malware that encrypts a victim’s data and demands payment for its release. This method has seen significant evolution with tactics like double extortion.
Drive-By Attacks
These occur when a user unknowingly visits a compromised website, leading to the automatic installation of malware onto their device.
Zero-Day Exploits
Attackers exploit a security vulnerability on the same day it is discovered before you can implement a patch or solution.

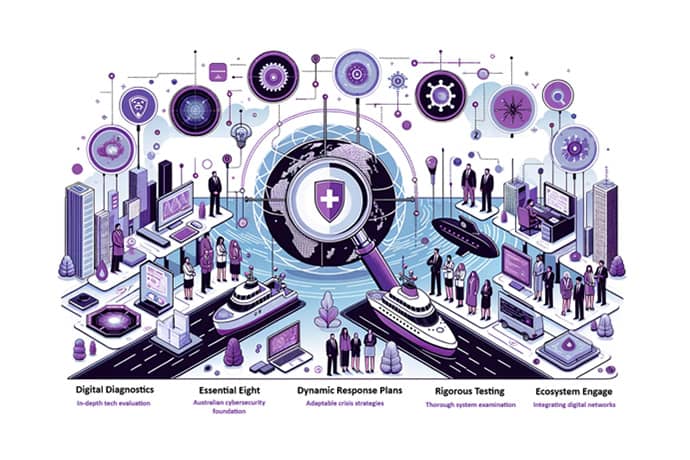
Planning Cyber Resilience
1. Digital Diagnostics - Guaging Cyber Maturity
- Before charting a way forward, we need to know where you stand. Assess your cyber maturity by evaluating your organisation’s rules, processes, and preparedness.
- Anchor your assessment using globally recognised frameworks like the NIST Cybersecurity Framework or ISO/IEC 20071:2022. Collaborate with cyber experts who can offer tailored recommendations based on these standards.
- For those overseeing critical infrastructure assets under Australia’s Security of Critical Infrastructure Act 2018, ensure your strategies align with the Critical Infrastructure Risk Management Plan requirements.
2. The Australian Baseline - Essential Eight
- The Australian Cyber Security Centre’s Essential Eight offers mitigation strategies tailored for Australian businesses. Don’t write it off as a mere checklist.
- While the Essential Eight caters primarily to Windows-based networks, the digital world is vast. If your ecosystem encompasses cloud services or enterprise mobility, you must seek strategies tailored to these environments.
3. Dynamic Response Plans - Shielding Against Digital Incidents
- It’s not about ‘if’ but ‘when’ a cyber incident will occur. A response plan ensures that when the inevitable strikes, you’re not reacting but responding with a well-thought-out strategy.
- While the KWM’s Cyber Response Guide is a good starting point, tailor your response plan to your organisation’s unique aspects, considering specific assets, stakeholders, and potential vulnerabilities.
4. Rigorous Testing - Key to Robustness
- A plan is as good as its execution. Regular testing makes sure that the theoretical strategies translate to practical effectiveness.
- Engage in controlled, simulated cyber attacks. Such ‘war games’ test systems and decision-making capabilities under pressure, ensuring that when a real threat emerges, your organisation is battle-ready.
5. Ecosystem Engage - The Culture
- A cyber-resilient culture starts with its people. Regular training sessions should be the norm, especially on prevalent threats like phishing. Make cyber awareness an integral part of your organisational culture.
- Ensure clarity on roles during a cyber incident. Everyone from the IT team to the C-suite should know their part, ensuring a swift and coordinated response.

Intensifying ‘Cyber Wargaming’ in the wake of rising threats
Australia is now under the spotlight for a vastly different reason – an intensified focus on cyber resilience. Recent cyberattacks on major Australian entities have underscored the need for bolstered defenses and heightened preparedness.
One of the cornerstone initiatives is the introduction of ‘wargaming’ exercises aimed at improving cyber resilience by using simulated cyberattacks involving major banks and institutions. It aims to test and refine response strategies in real-time scenarios.
Banking Sector
Banks are the primary wealth-keeping entity for an average Australian. They offer a protective vault for your financial wealth, fostering a deep sense of trust. As a result, one might keep a significant, if not the entire, portion of their wealth there. However, this very trust makes banks a prime target for cybercriminals. Your wealth – protected by a series of numbers in the form of account details and PIN codes, can be a few steps away from a major attack.
Distributed Denial of Service (DDoS)
What it Looks Like
Overwhelming traffic sent to a bank’s website or online service.
Impact
It can crash the bank’s online services, preventing customers from accessing their accounts.
Advanced Persistent Threat (APT)
What it Looks Like
Highly Sophisticated, long-term cyberattacks.
Impact
Allows criminals to gain deep access, stealing vast amounts of financial data or funds over time.
Man-in-the-Middle (MitM) Attack
What it Looks Like
Attackers can use malicious code to exploit database weaknesses.
Impact
It can give access to the bank’s database, potentially leaking large amounts of data.
Zero-Day Exploit
What it Looks Like
Taking advantage of software vulnerabilities before the bank or software provider knows or can fix them.
Impact
Immediate and unexpected theft or damage, as defences aren’t yet in place.
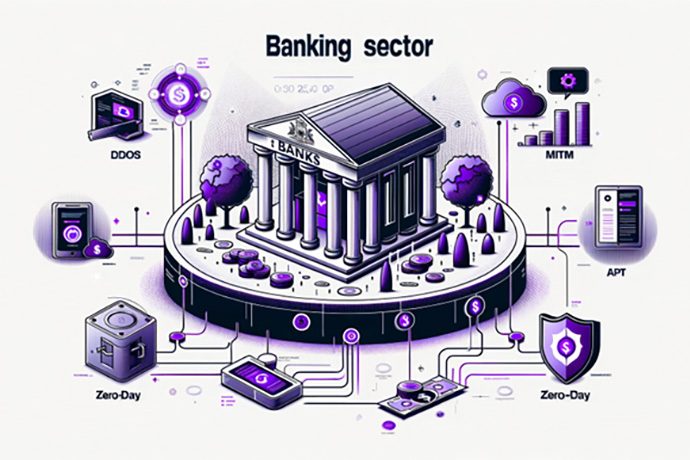
The Latitude Financial incident, where 14 million customer records were stolen, further highlights the audacity and capability of cybercriminals. Although rejected in line with government policy, their ransom demands underline the urgent need for fortified defences.
Telecommunications Sector
Telecommunication providers like Telstra and Vodafone connect us to our loved ones, facilitate business and operations, and entertain us through various digital channels. Given the nature of this service, telecom providers have become the backbone of contemporary communication, yet their role also means they become attractive targets for cybercriminals. These attackers are drawn to the vast amounts of personal data, communication logs, and financial transactions processed by telecom networks.
Eavesdropping Attack
What it Looks Like
Unauthorised interception of calls or messages.
Impact
Privacy breach, leading to the leak of sensitive personal or business information.
SIM Swapping
What it Looks Like
Attackers can deceive telecom providers to issue a new SIM card in the victim’s name.
Impact
The attacker gains control of the victim’s phone number, allowing unauthorised access to calls, texts, and two-factor authentication codes.
Infrastructure Tampering
What it Looks Like
Physical or digital interference with telecom hardware.
Impact
It can cause network outages, slow services, or provide unauthorised access to sensitive telecom network parts.
Malware and Spyware
What it Looks Like
Harmful software introduced into telecom infrastructure.
Impact
It can monitor user activity, steal data, or disrupt services.
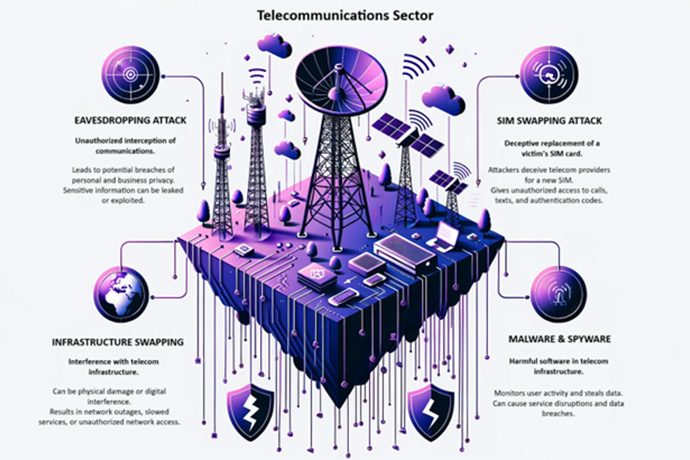
Optus, one of Australia’s leading telecommunications providers, experienced a significant cyber breach. Attackers accessed the personal details of approximately 10 million customers, including names, birth dates, phone numbers, and crucial identity documents. This prompted nationwide concern, leading to governmental involvement, discussions on privacy laws, and calls for increased cybersecurity measures.
Health Insurance Sector
Health insurance providers have somewhat of a dual role:
A. They must facilitate medical coverage and care for millions
B. They must act as guardians of highly sensitive personal and medical data.
This data, often including everything from basic identification details to comprehensive medical histories, represents a goldmine for cybercriminals. It can result in a lot of threatening production of non-regulated drugs and is overall a huge privacy issue.
Data Breach
What it Looks Like
Unauthorised access to databases, leaking private customer information.
Impact
Exposed personal and medical details of customers, risking identity theft and privacy invasion.
Ransomware Attack
What it Looks Like
Malicious software locks out legitimate users until a ransom is paid.
Impact
Potentially halting medical services or access to patient data until demands are met.
Phishing Scam
What it Looks Like
Deceptive emails or messages impersonating the health insurer.
Impact
Deceived individuals might provide personal or financial data directly to criminals.
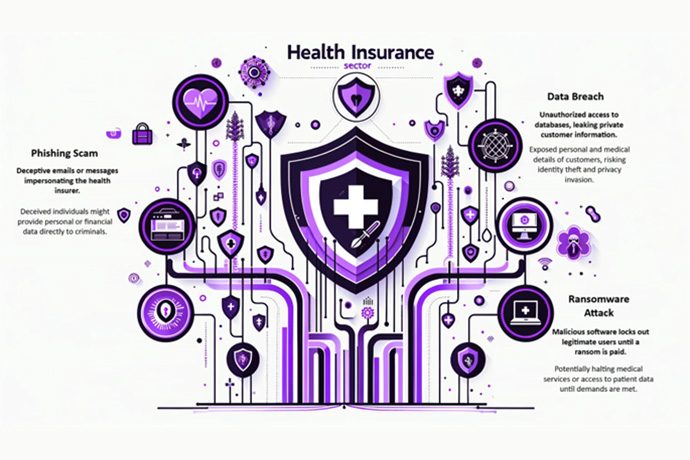
In a recent and significant breach, Medibank faced a massive cyber attack, resulting in the personal details of nearly 10 million customers being exposed on the dark web. This included data from 9.7 million current and former customers, including:
- 5.1 million Medibank clients
- 2.8 million AHM clients
- 1.8 million international clients
The breach led to a class action lawsuit by Backer McKenzie, spotlighting the company’s alleged failure to protect customer privacy.
Home Affairs Minister Clare O’Neil’s warning serves as a clarion call, emphasising the recent cyber incidents are mere glimpses of potential larger-scale threats. As Anna Bligh, CEO of the Australian Banking Association, rightly pointed out, the evolving nature of cyber threats now poses risks that transcend corporate boundaries, potentially jeopardising national security.
Conclusion
In essence, the emphasis on cyber resilience underscores the nation’s commitment to ensuring business continuity and protecting its citizens’ digital assets and information. The digital future is bright only if we do our due diligence. Want to make your company cyber-resilient? Talk to our experts at LEAP Strategies and pave your way toward a cyber-resilient future!
References
- Terranova Security. “60% of Small Businesses Go Out of Business After a Cyber Attack.”
- Australian Cyber Security Centre (ACSC). (2017). “Essential Eight Maturity Model”
- NIST. (2018). “Framework for Improving Critical Infrastructure Cybersecurity”
- ISO/IEC. (2022). “ISO/IEC 20071:2022 – Information technology — Security techniques — Cybersecurity framework development guidelines”
- Australian Government. (2018). “Security of Critical Infrastructure Act 2018”
- King & Wood Mallesons (KWM). (2023). “Cyber Response Guide”
- Australian Banking Association. (2020-2024). “Cybersecurity and the Banking Sector”
- Telstra. (2019). “Annual Cybersecurity Report”
- Vodafone. (2023). “Cybersecurity and Telecommunications: Safeguarding our Networks”
- Medibank. (2022). “Statement on recent cyber incident”
- Backer McKenzie. (2023). “Class action lawsuit against Medibank”
- O’Neil, Clare. (2023). “Statement on Cybersecurity in Australia”
- Bligh, Anna. (2023). “Cybersecurity and the Banking Sector: A National Concern”





