Deconstructing the DDoS attack
There’s nothing worse than events disrupting your ability to run your business. A Disrupted Denial of Service (DDoS) attack has emerged as a pervasive and potent cyber threat to businesses everywhere.
Understanding a DDoS Attack
A Distributed Denial of Service, a DDoS attack, is a malicious attempt to disrupt the regular functioning of a network, service, or website by overwhelming it with a flood of traffic. This inundation attack, generally orchestrated by an extensive network of compromised computers, renders the targeted system inaccessible.
This cyber attack is problematic because the disruption can last anywhere from a few minutes to a day or two. This mitigable disruption can cause financial and reputational damage to a business, which can be hard to recover from. DDoS attacks have also been commonly used as a precursor or distraction so an adversary can execute a more significant cyber attack.
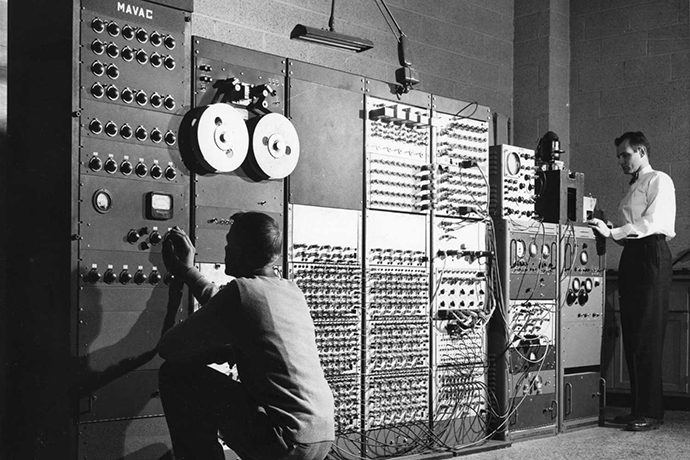
A brief history of the DDoS attack
In 1999, cyber attackers coined the term DDoS to describe using more sophisticated tools to disrupt computer systems. Before DDoS, DoS relied on multiple users logging onto computers to execute a simple attack.
These days, we distinguish DDoS and DoS by networks used in the attack, where DoS attacks originate from a single internet network, while DDoS requires far more computer power.
Some may think DDoS attacks have emerged with the rapid evolution of computers, technology and the cybersecurity industry. Although true, DDoS has evolved from a simple Denial of Service (DoS) attack against early computerised systems between 1974 and 1999.
Targeting Protocols
To pull off a DDoS attack, you first need a bot army, built through clever tactics like phishing or exploiting vulnerabilities. It’s all about crafting a vast web of Botnets – networks of hijacked computers (aka zombies) – all controlled by one mastermind for coordinated cyber onslaughts.
Six potential ways exist for attackers to target various protocols.
UDP Floods
UDP (User Datagram Protocol) floods are a type of DDoS attack where a large volume of UDP packets is sent to a target system, overwhelming its capacity to handle incoming requests.
Since UDP is connectionless and does not require a handshake process, attackers can flood the target with numerous UDP packets, leading to resource exhaustion and service disruption.
SYN Floods
SYN (Synchronise) floods exploit the three-way handshake process of the TCP (Transmission Control Protocol) to overwhelm a target server.
Attackers flood the target with a high volume of TCP SYN requests but do not complete the handshake, leaving the server waiting for a response that never comes. This exhausts the server’s resources and can lead to denial of service.
NTP Amplification
NTP (Network Time Protocol) amplification attacks involve exploiting vulnerable NTP servers to amplify the volume of traffic directed at a target.
Attackers send small requests to NTP servers with the target’s address as the source, causing the NTP servers to respond with larger data packets. This amplification effect results in a deluge of traffic directed at the target, overwhelming its capacity.
DNS Amplification
DNS (Domain Name System) amplification attacks leverage insecure DNS servers to amplify the volume of traffic directed at a target.
Attackers send small DNS queries to vulnerable servers with the target’s address as the source, prompting the servers to respond with larger data packets. This amplification leads to a significant increase in traffic directed at the target, causing service disruption.
SSDP Amplification
SSDP (Simple Service Discovery Protocol) amplification attacks exploit vulnerable SSDP servers to amplify the volume of traffic directed at a target.
Like other amplification attacks, the attacker sends small requests to SSDP servers with the target’s address as the source, causing the servers to respond with larger data packets. This amplification magnifies the impact of the attack on the target.
SYN-ACK floods
SYN-ACK (Synchronise-Acknowledge) floods are a variant of SYN floods where the attacker sends a large volume of SYN-ACK packets to a target server. This overwhelms its resources.
In this scenario, the attacker completes the TCP three-way handshake, leading the server to allocate resources for connections that were never initiated. This results in resource exhaustion and service disruption for the targeted system.

Motivations Behind DDoS Attacks
So why do attackers choose to execute a DDoS attack? At a basic level, many DDoS attackers will be motivated by:
- Financial gain where extortionists demand payment to cease the attack
- Ideological motives from activists to target organisations aligning with opposing ideologies
- Competitor interference from businesses who might deploy DDoS attacks to take down their competitors’ online services for their gain
However, the psychology of DDoS attacks runs deeper, where the scope of motivations is broad. Dutch researchers Deshmukh and Devadkar in 2015 broke down eight deeper motivations with supportive sub-motives behind DDoS attacks.
If you need a technology management partner who can guide you on how to shield your business from DDoS attacks best, Leap Strategies can tailor solutions to put you ahead of the game before any shots are fired.
Conclusion
DDoS attacks persist as an enduring challenge and will only become more sophisticated. The threat landscape remains dynamic, from the historical notoriety of impactful incidents to the evolving strategies employed by attackers. Implementing robust prevention and mitigation strategies is imperative. As technology advances, so must our defences against the relentless tide of DDoS attacks.





